Introduction
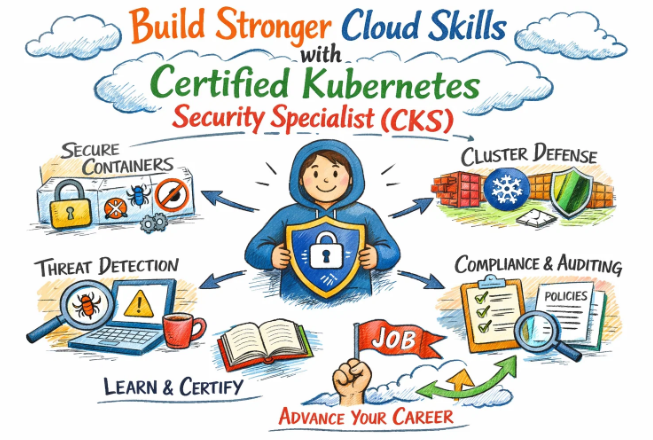
In the current landscape of cloud computing, the protection of digital assets is considered a top priority. As more organizations transition to containerized environments, the security of those systems is viewed as a fundamental necessity. The Certified Kubernetes Security Specialist (CKS) is recognized as a premier credential that validates a professional’s ability to safeguard these complex infrastructures. This guide is provided to help software engineers and managers understand the depth, value, and path associated with this advanced certification.
What is Certified Kubernetes Security Specialist (CKS)?
The CKS is defined as a performance-based certification that focuses on the security of container-based applications. It is administered by the Cloud Native Computing Foundation (CNCF) and the Linux Foundation. Unlike traditional exams, the CKS is conducted in a live, simulated environment where practical tasks must be solved within a two-hour window. It is specifically designed to test competencies across the entire development and deployment lifecycle, from building secure images to monitoring active clusters.
Why it matters in today’s software, cloud, and automation ecosystem
Security is no longer seen as an optional layer; it is now woven into the fabric of automation and cloud services. As clusters become more complex, the risk of misconfiguration is heightened. The CKS matters because it provides a standardized methodology for reducing attack surfaces. By obtaining this certification, a professional is acknowledged as someone who can implement “Defense in Depth” strategies. This ensures that even if one layer of a system is breached, additional safeguards are maintained to protect sensitive data.
Why certifications are important for engineers and managers
For engineers, certifications are used to demonstrate technical proficiency in a competitive job market. It allows a specialist to be distinguished as a reliable expert who can manage production-level risks. For managers, the presence of certified individuals on a team is seen as a way to reduce organizational liability. When a standardized knowledge base is shared across an engineering team, communication is improved, and security protocols are implemented more consistently.
Why Choose DevOpsSchool?
The selection of DevOpsSchool is often driven by its reputation for high-quality technical mentorship. Students are provided with comprehensive training that is rooted in real-world scenarios rather than just theoretical concepts. Access to expert-led sessions, updated study materials, and practical lab environments is ensured. Furthermore, guidance is offered by instructors who possess extensive industry knowledge, making the learning journey more efficient and result-oriented for professionals worldwide.
Certification Deep-Dive: Certified Kubernetes Security Specialist (CKS)
What is this certification?
This is an advanced-level credential that verifies a candidate’s mastery of Kubernetes security. It is focused on the practical application of security best practices across all stages of a containerized application’s life.
Who should take this certification?
This path is recommended for those who have already completed the Certified Kubernetes Administrator (CKA) exam. It is ideally suited for Security Engineers, DevOps practitioners, and Platform Architects who are responsible for cluster integrity.
Certification Overview Table
| Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
| DevOps | Advanced | Platform Engineers | CKA | Pipeline Security | Post-CKA |
| DevSecOps | Expert | Security Leads | CKA | Vulnerability Management | Mandatory |
| SRE | Advanced | Reliability Leads | CKA | Runtime Monitoring | Post-CKA |
| AIOps/MLOps | Advanced | ML Engineers | CKA | Data Pipeline Security | Optional |
| DataOps | Advanced | Data Architects | CKA | Encryption at Rest | Optional |
| FinOps | Advanced | Cloud Controllers | CKA | Resource Governance | Strategic |
Skills you will gain
- Cluster components are hardened against unauthorized access.
- Network policies are implemented to isolate workloads.
- Container images are scanned for critical vulnerabilities.
- Runtime security events are detected using specialized tools.
- Static analysis of YAML files is performed to ensure compliance.
- Secrets are managed securely within the Kubernetes environment.
- The host operating system is secured by reducing its footprint.
Real-world projects you should be able to do after this certification
- A fully secured CI/CD pipeline is built with automated image signing.
- A zero-trust network architecture is established within a multi-tenant cluster.
- Runtime threat detection is configured to alert on suspicious container activity.
- A compliance audit is performed against CIS Kubernetes benchmarks.
- Admission controllers are used to enforce security policies across all deployments.
Preparation Plan
7–14 Days Plan
- Foundational CKA knowledge is reviewed.
- Familiarity with the official Kubernetes documentation is developed.
- Network Policy configuration is practiced daily.
- The basic use of tools like Trivy and Falco is mastered.
30 Days Plan
- Two hours are dedicated each day to hands-on lab exercises.
- The six exam domains are studied in weekly blocks.
- Mock exams are used to build speed and accuracy in a terminal environment.
60 Days Plan
- Deep exploration of kernel-level security tools like AppArmor is conducted.
- Complex security scenarios involving multi-pod communication are practiced.
- A full-scale secure cluster is built from scratch multiple times to ensure mastery.
Common mistakes to avoid
- The prerequisite of basic Linux security is often neglected.
- Too much time is spent on a single difficult question during the exam.
- Implicit default settings in Kubernetes are assumed to be secure.
- The use of imperative commands is not practiced enough for speed.
- Documentation search skills are not refined before the test date.
Best next certification after this
- Same track: Specialized cloud security certifications (e.g., AWS Security).
- Cross-track: Certified Kubernetes Application Developer (CKAD) for a broader view.
- Leadership / management: IT leadership or Strategic Cloud Management programs.
Choose Your Learning Path
DevOps Path
This path is chosen by those who want to automate security within the delivery cycle. It is best for professionals focused on speed and safety.
DevSecOps Path
This is selected by specialists who aim to make security a core feature of the development culture. It is suitable for those leading security transformations.
Site Reliability Engineering (SRE) Path
The focus here is on maintaining system uptime through secure practices. It is ideal for engineers who view security as a key component of reliability.
AIOps / MLOps Path
This is followed by those who secure the data and models used in AI systems. It is best for data-focused engineers in cloud environments.
DataOps Path
The protection of data integrity and privacy is prioritized here. This path is intended for architects managing large-scale data workloads.
FinOps Path
Security is managed from a cost-optimization perspective. This is best for professionals who ensure that security measures do not lead to financial inefficiency.
Role → Recommended Certifications Mapping
| Role | Recommended Certification | Purpose |
| DevOps Engineer | CKS | Automation Security |
| SRE | CKS | System Resilience |
| Platform Engineer | CKS | Foundation Hardening |
| Cloud Engineer | CKS | Infrastructure Trust |
| Security Engineer | CKS | Core Competency |
| Data Engineer | CKS | Information Protection |
| FinOps Practitioner | CKS | Governance & Control |
| Engineering Manager | CKS (Basics) | Risk Assessment |
Next Certifications to Take
For the DevOps Learner:
- Same-track: Terraform Certification
- Cross-track: Certified Cloud Architect
- Leadership: Agile Project Management
For the Security Specialist:
- Same-track: Offensive Security Practitioner
- Cross-track: Solutions Architect (Professional)
- Leadership: Risk Management Professional
For the Platform Engineer:
- Same-track: Istio or Service Mesh Specialist
- Cross-track: Linux Engineer (Advanced)
- Leadership: Team Leadership for Engineers
Training & Certification Support Institutions
DevOpsSchool
Extensive training programs are offered here with a focus on career growth. Practical knowledge is emphasized through hands-on projects.
Cotocus
A personalized approach to technical learning is provided. Expertise in cloud technologies is shared through structured workshops.
ScmGalaxy
Valuable community resources and tutorials are maintained for the benefit of engineers. A strong focus on modern tooling is observed.
BestDevOps
The gap between learning and employment is bridged by this institution. Intensive training is conducted to prepare students for real-world roles.
devsecopsschool.com
A dedicated platform for security-integrated operations. Courses are tailored for the modern DevSecOps landscape.
sreschool.com
Reliability engineering principles are taught here. The connection between stability and security is explored in detail.
aiopsschool.com
Innovative training on AI-driven operations is provided. The future of automated infrastructure is the primary focus.
dataopsschool.com
Best practices for data-centric operations are taught. The challenges of modern data security are addressed.
finopsschool.com
The financial aspect of cloud engineering is mastered here. Professionals are taught to manage cloud budgets effectively.
FAQs Section
1. Is the CKS exam purely theoretical?
No, it is a 100% hands-on, performance-based assessment.
2. What is the required score to pass?
A passing mark of 67% must be achieved.
3. Is CKA required before taking CKS?
Yes, the CKA must be completed, though it does not need to be active at the time of the CKS exam.
4. How is the exam conducted?
The exam is proctored online through a secure browser environment.
5. What is the validity of the CKS certificate?
The credential is valid for a period of two years.
6. Are cloud-specific tools tested?
The focus is on open-source and Kubernetes-native security tools.
7. Can the exam be retaken?
One free retake is typically included with the purchase of the exam.
8. Is the use of official documentation permitted?
Yes, specific Kubernetes documentation sites are allowed during the test.
9. How long does the exam session last?
A total of two hours is provided to complete the tasks.
10. What level of Linux knowledge is needed?
An intermediate understanding of Linux system administration is highly recommended.
11. Is the CKS relevant for junior engineers?
It is more suited for mid-to-senior level engineers due to its complexity.
12. Does CKS cover application-level security?
Yes, it includes topics like image scanning and microservice vulnerability management.
Additional FAQs: Certified Kubernetes Security Specialist (CKS)
- Is Falco included in the CKS curriculum?
Yes, runtime security monitoring with Falco is a key part of the exam. - Are Pod Security Policies still tested?
No, they have been replaced by Pod Security Admissions in recent versions. - Is image signing covered?
Yes, the concepts of image provenance and signing are included in the supply chain domain. - Can I use an external monitor during the exam?
Only one monitor is permitted as per the standard proctoring rules. - Is OPA Gatekeeper a part of the exam?
Yes, the use of admission controllers like OPA is frequently tested. - How often is the CKS exam updated?
The curriculum is updated to align with the latest stable Kubernetes releases. - Is secret encryption tested?
Yes, the encryption of secrets at rest in etcd is a common task. - Will passing the CKS renew my CKA?
No, passing the CKS does not extend the validity of a CKA certification.
Testimonials
The practical skills needed to secure a cluster were mastered through this training. A high level of confidence was gained before attempting the exam. — Kavita
A total shift in perspective regarding cloud-native security was experienced. The guidance provided was instrumental in achieving success on the first attempt. — Siddharth
The hands-on labs were considered the most helpful part of the course. Real-world challenges were simulated effectively, leading to a deeper understanding. — Ananya
A professional advantage was secured in the job market after obtaining the CKS. The focus on best practices was appreciated and applied in daily work. — Manish
The journey from a basic administrator to a security specialist was made possible by the structured path provided. Every session was found to be highly valuable. — Priyanka
Conclusion
The importance of the Certified Kubernetes Security Specialist (CKS) certification is highlighted by the growing demand for secure cloud infrastructure. It is established as a vital milestone for any professional seeking to excel in modern engineering roles. Long-term career stability and growth are achieved by those who prioritize the mastery of these security principles. Strategic planning for this certification is encouraged for all who aim to build a future in a safe and resilient digital world.